The Privileged Access Blog
The Migus Group’s blog covering identity and access management, PAM, DevSecOps, IT operations and other topics related to enterprise security.

What Is Information Security, and How Does It Affect Your Business? — December 20, 2022
What is information security? Explore the challenges of data protection and learn how an effective strategy can reduce your risks.

How To Build Cyber Resiliency in Your Business — December 19, 2022
Cyber resiliency for today’s businesses is as crucial as having a top-notch screening process for your top-level employees. Assess your preparedness today.

Incident Response Planning: Important Tips for Active Directory Users — December 13, 2022
Ensure Active Directory access with an effective incident response plan. Learn how to prepare and respond to a security event.

MFA Statistics and Trends Every Business Leader Should Know — December 6, 2022
Multifactor authentication (MFA) exists to protect you by balancing security and convenience. Modern-day MFA utilizes digital sophistication in an attempt to stay one step ahead of cybercriminals and bad actors. Consider the following MFA statistics and trends.

How To Secure Your Business With a Privileged Identity Management Solution — November 29, 2022
Privileged identity management, or PIM, gives IT administrators the ability to control, manage and monitor the access privileges that users have to critical resources within an organization.

4 Uses for Cybersecurity Risk Assessments — November 14, 2022
Cybersecurity risk assessments are used to identify your most important data and devices, how a hacker could gain access, what risks could crop up if your data fell into the wrong hands, and how vulnerable your organization would be as a target.
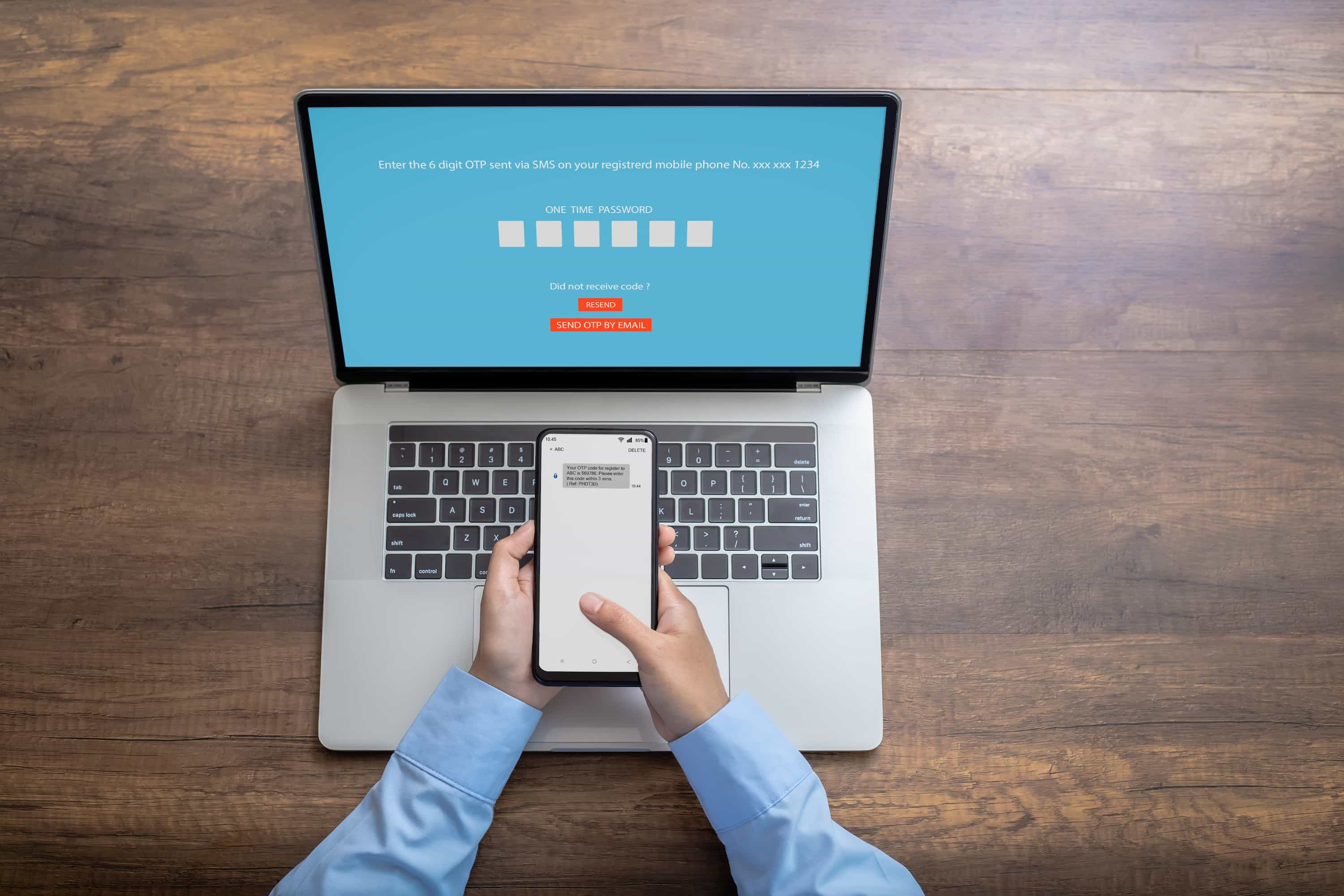
MFA-Enabled vs. Enforced: Which Works Best for Your Company? — November 8, 2022
Is there a difference between MFA enabled vs. enforced? Learn which multifactor authentication approach works best for your company.

5 Active Directory Alternatives — November 1, 2022
Does your access management system feel outdated? Discover five Active Directory alternatives that improve workflows and reduce costs.

Identity and Access Management Tools to Keep in Your IT Toolkit — October 18, 2022
Considering IAM? We’ve compiled a list of some of the best identity and access management tools that we work with and provide useful information on each of them for you.

An Overview of IAM Security — October 11, 2022
IAM security is a framework of processes, policies and systems that manage digital identities in a highly secure, streamlined manner.