The Privileged Access Blog
The Migus Group’s blog covering identity and access management, PAM, DevSecOps, IT operations and other topics related to enterprise security.

How Zero Trust Network Access Improves Security — October 3, 2022
A newer security concept known as zero trust network access (ZTNA) hides the network location — the IP address — and instead uses identity-based authentication to establish trust and provide access. As a result, ZTNA provides centralized control and improved flexibility to secure highly distributed IT environments.

IAM vs. PAM: What Can They Do for Your Business? — September 20, 2022
IAM and PAM are two types of access-management strategies that organizations use to manage authentication and authorization at scale. However, while similar, these products serve very different functions within an enterprise IT environment.

How To Secure Your Credentials With a PAM Solution — September 13, 2022
Identifying a PAM solution is a strategy to secure, control and monitor access to an organization’s critical information and resources.

How To Choose the Best MFA Solution for Your Business — September 6, 2022
MFA is a security strategy requiring multiple methods of authentication of a user’s credentials in order to verify that user’s identity for a login or other type of access. Identifying the best MFA solution for your business is crucial.

Why MFA Is the Key to Securing Small Businesses — August 30, 2022
Unfortunately, the benefits of multi-factor authentication are not as widespread among SMBs, who are increasingly vulnerable to cyberattacks.

What Is FIDO2, and How Does It Work? — August 23, 2022
FIDO2 is the umbrella term for an open standard for authentication that does not rely on passwords.
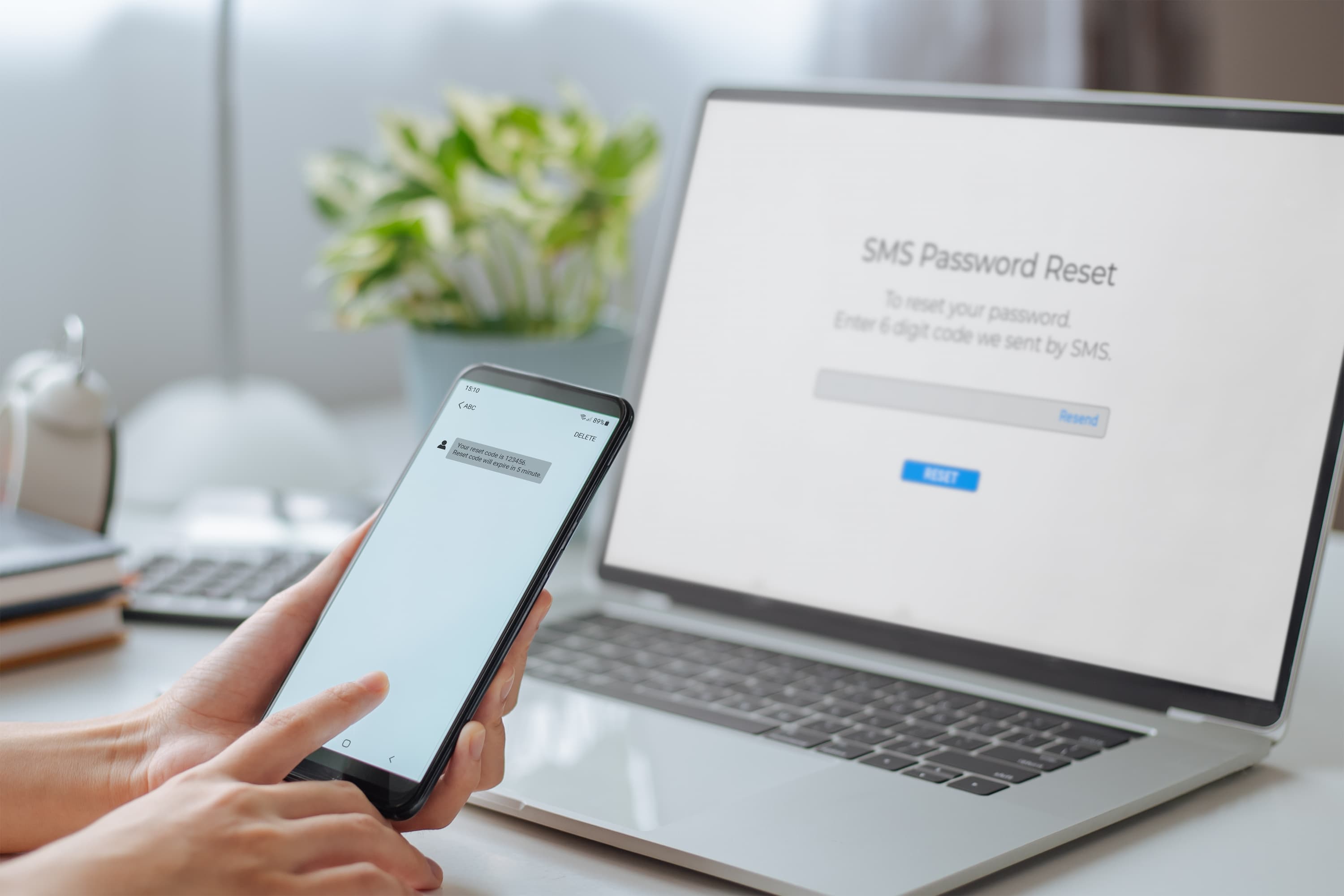
MFA vs. 2FA: What’s the Difference? — August 16, 2022
Because single-factor authentication has proven to be relatively easy to compromise, two-factor authentication (2FA) and multifactor authentication (MFA) have emerged as more secure options. Read on to learn about common authentication types, the differences in MFA vs. 2FA and more

Why Every Leader Should Understand Zero Standing Privilege — August 9, 2022
Zero standing privilege (ZSP) is a security policy that no users should be pre-assigned any administrative account privileges. Instead, with ZSP, users’ privileges are assigned at the moment of the attempt to authenticate — not beforehand and not by default.

Universal 2nd Factor (U2F): The Importance of Security Keys — August 3, 2022
Universal 2nd Factor (U2F) is a physical authentication device that uses encryption and private keys to protect and unlock supported accounts. Read on to understand their significance

5 Best Practices of Open-Source Management — July 19, 2022
Open-source management essentially means keeping the project up to date so that it is compatible with the latest version of the various third-party libraries, frameworks and software that it uses. It’s equally important to be mindful of good, strong security measures.