Data breaches impacted nearly 6 million accounts in 2021. The human factor plays a significant role, with more than 80% of basic web application attacks (BWAA) stemming from stolen credentials. Multifactor authentication (MFA) tools can reduce risks. However, you must choose between MFA-enabled and enforced.
User roles, data types and applications will affect this decision. Understanding the distinction between the two helps you balance security with user experience. Learn about the difference between MFA-enabled and -enforced tools and how to choose the best methods for managing end-user network access.
MFA-Enabled vs. Enforced: What’s the Difference?
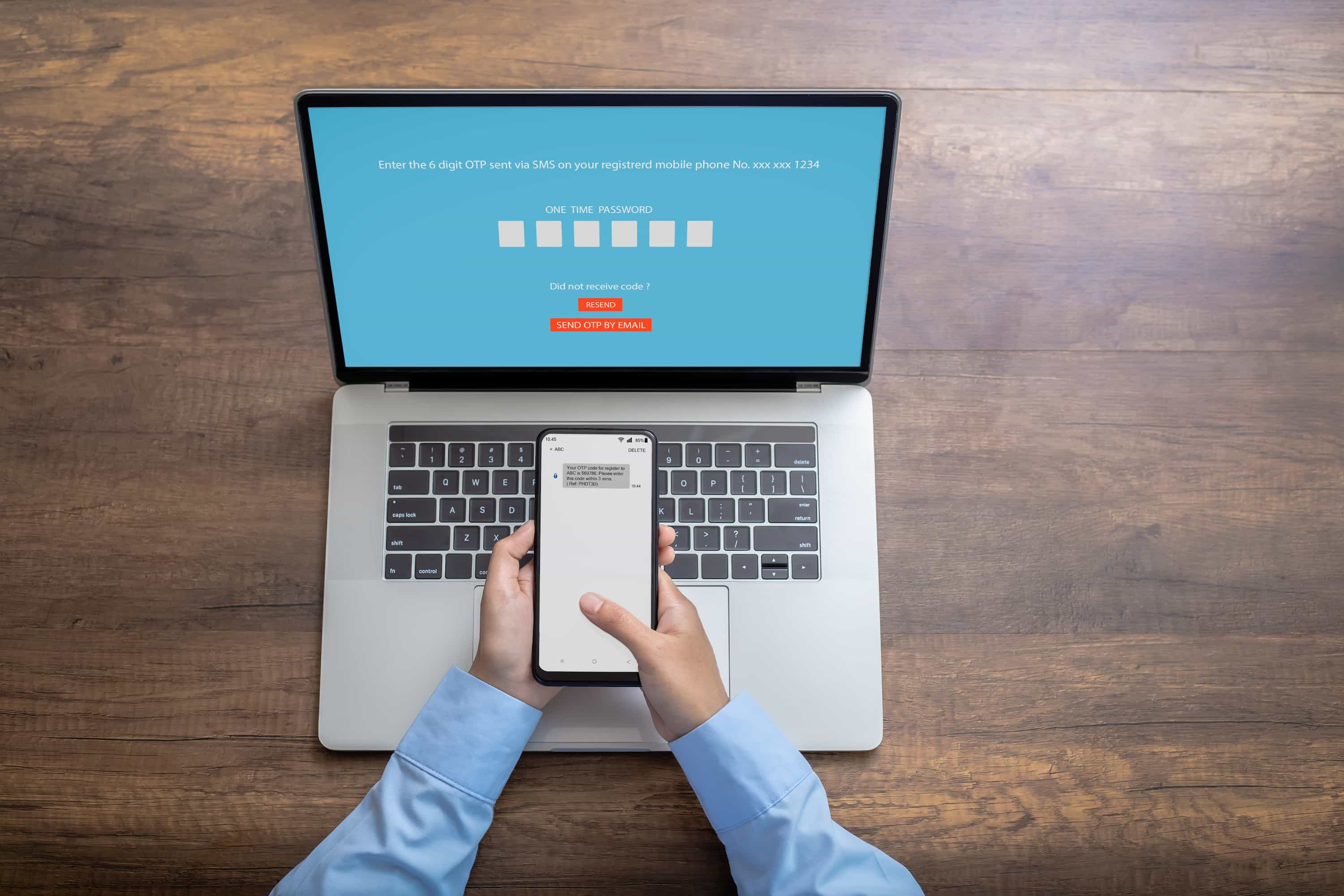
The bottom line is that “MFA-enabled” means the authentication tool is available, whereas “MFA-enforced” requires its usage. When you enable MFA, you set up the authentication methods (ways to confirm identity) and suggest employees register. But you don’t necessarily block non-MFA users from accessing your network and applications.
In comparison, when you enforce MFA, employees, contractors and other third parties must use MFA when logging into your system and related platforms. Since this can be tedious, some organizations are adopting adaptive MFA solutions which use all MFA protocols but add a third authentication depending on how the user logs in.
Many software programs allow administrators to enable MFA in a company-wide, per-user or role-based manner. But not all automatically enable MFA, meaning you will need to turn on the service manually. Likewise, some software vendors let you turn on MFA enforcement, and increasingly, they are making it a requirement to use their products.
For instance, Salesforce recently told clients that they are “contractually required to use MFA to access Salesforce products.” To this end, Salesforce is automatically enabling MFA. The company is also rolling out enforcement measures, “making it a permanent part of the direct login process and removing controls for admins to disable it.”
How To Choose the Right MFA Solution
As Verizon notes, poor password practices have been “one of the leading causes of data breaches dating back to 2009,” with a “30% increase in stolen credentials” since 2017. Yet, Microsoft acknowledges that “your account is more than 99.9% less likely to be compromised if you use MFA.”
For this reason and many others, requiring two or more authentication methods can strengthen your organization’s security posture. Enablement and enforcement methods vary among software providers, including identity access and management (IAM) tools. Requiring MFA is the most secure option because unregistered users can’t access business networks or applications.
However, you may want an adjustment period with MFA-enabled before mandating it. This can help employees acclimate and let your IT team work out the kinks. The best MFA solution provides a seamless user experience without sacrificing security. Reviewing your options before making a decision is crucial to meet both needs.
Deciphering Authentication Factors and Situations
You have many options when it comes to managing network and application access. Individual platforms allow you to make MFA optional or required, but the security level varies by subscription tier and vendor. Identity management services work with multiple tools, but capabilities and integrations differ among providers.
Some security technologies support rolling codes and number matching. Others use push notifications, which are vulnerable to MFA spamming, also known as MFA fatigue. Adaptive MFA gives you more flexibility by considering how the user accesses the system. For example, adaptive MFA technology can recognize a hybrid worker’s secure office network and allow login but require MFA when that same person uses public Wi-Fi.
Plus, you may want a more straightforward solution for specific roles or applications. Consider two-factor authentication (2FA) over MFA for applications that don’t store sensitive data instead of enforcing MFA.
Understand How MFA Fits Into Your IAM Policies
Stolen credentials remain the top threat to your network security. Enabling MFA is an excellent first step to improving your security posture. Although MFA enforcement provides a higher security level, user experience factors must be considered. It can be challenging to find the right multifactor authentication solution. The Migus Group can help you compare MFA-enabled vs. enforced products and determine how they fit into your identity and access management policies. Learn more by contacting us today.
Jessica Elliott is a business technology writer specializing in cloud-hosted and cybersecurity services. Her work appears in U.S. News, Business.com and Investopedia.